In this post, we present our new Burp Suite extension "TLS-Attacker".
Using this extension penetration testers and security researchers can assess the security of TLS server configurations directly from within Burp Suite.
The extension is based on the TLS-Attacker framework and the TLS-Scanner, both of which are developed by the Chair for Network and Data Security.
You can find the latest release of our extension at: https://github.com/RUB-NDS/TLS-Attacker-BurpExtension/releases

Furthermore, the extension allows fine-tuning for the configuration of the underlying TLS-Scanner. The two parameters parallelProbes and overallThreads can be used to improve the scan performance (at the cost of increased network load and resource usage).
It is also possible to configure the granularity of the scan using Scan Detail and Danger Level. The level of detail contained in the returned scan report can also be controlled using the Report Detail setting.
Please refer to the GitHub repositories linked above for further details on configuration and usage of TLS-Scanner.
This is a combined work of Nurullah Erinola, Nils Engelbertz, David Herring, Juraj Somorovsky, Vladislav Mladenov, and Robert Merget. The research was supported by the European Commission through the FutureTrust project (grant 700542-Future-Trust-H2020-DS-2015-1).
If you would like to learn more about TLS, Juraj and Robert will give a TLS Training at Ruhrsec on the 27th of May 2019. There are still a few seats left.
Continue readingUsing this extension penetration testers and security researchers can assess the security of TLS server configurations directly from within Burp Suite.
The extension is based on the TLS-Attacker framework and the TLS-Scanner, both of which are developed by the Chair for Network and Data Security.
You can find the latest release of our extension at: https://github.com/RUB-NDS/TLS-Attacker-BurpExtension/releases
TLS-Scanner
Thanks to the seamless integration of the TLS-Scanner into the BurpSuite, the penetration tester only needs to configure a single parameter: the host to be scanned. After clicking the Scan button, the extension runs the default checks and responds with a report that allows penetration testers to quickly determine potential issues in the server's TLS configuration. Basic tests check the supported cipher suites and protocol versions. In addition, several known attacks on TLS are automatically evaluated, including Bleichenbacher's attack, Padding Oracles, and Invalid Curve attacks.

Furthermore, the extension allows fine-tuning for the configuration of the underlying TLS-Scanner. The two parameters parallelProbes and overallThreads can be used to improve the scan performance (at the cost of increased network load and resource usage).
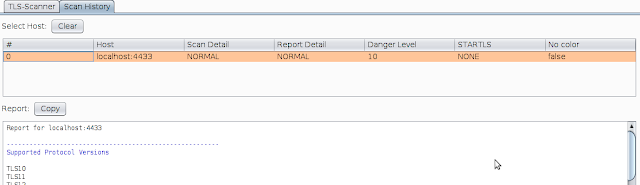
It is also possible to configure the granularity of the scan using Scan Detail and Danger Level. The level of detail contained in the returned scan report can also be controlled using the Report Detail setting.
Please refer to the GitHub repositories linked above for further details on configuration and usage of TLS-Scanner.
Scan History
If several hosts are scanned, the Scan History tab keeps track of the preformed scans and is a useful tool when comparing the results of subsequent scans.
Additional functions will follow in later versions
Currently, we are working on integrating an at-a-glance rating mechanism to allow for easily estimating the security of a scanned host's TLS configuration.This is a combined work of Nurullah Erinola, Nils Engelbertz, David Herring, Juraj Somorovsky, Vladislav Mladenov, and Robert Merget. The research was supported by the European Commission through the FutureTrust project (grant 700542-Future-Trust-H2020-DS-2015-1).
If you would like to learn more about TLS, Juraj and Robert will give a TLS Training at Ruhrsec on the 27th of May 2019. There are still a few seats left.
- Hack Website Online Tool
- Bluetooth Hacking Tools Kali
- Pentest Box Tools Download
- Nsa Hacker Tools
- Best Hacking Tools 2020
- Pentest Tools Online
- Hack And Tools
- Physical Pentest Tools
- Pentest Tools For Android
- Hacking Tools For Kali Linux
- Hacking Tools Windows
- Hacking Tools Name
- Android Hack Tools Github
- Pentest Tools Review
- Best Pentesting Tools 2018
- Pentest Tools Framework
- Tools 4 Hack
- Hacking Tools Usb
- Pentest Tools Windows
- Hack Tools Mac
- Pentest Tools Port Scanner
- Hacking Tools For Games
- Hack Tools 2019
- Hacking Tools 2020
- Pentest Tools Framework
- Hacker Tools Linux
- Bluetooth Hacking Tools Kali
- How To Make Hacking Tools
- Beginner Hacker Tools
- Pentest Tools
- Hacker Tools Hardware
- Hack Tools For Pc
- Hack Tools For Ubuntu
- New Hacker Tools
- Hacking Tools Free Download
- Hack Tools
- How To Hack
- Black Hat Hacker Tools
- Hacker Tools 2020
- Hacking Tools Download
- What Are Hacking Tools
- Hacker Tools Apk
- Physical Pentest Tools
- Pentest Tools
- Pentest Tools Kali Linux
- Hack Tools
- Hacker Tools For Mac
- Pentest Tools Kali Linux
- Hacking Tools 2020
- Pentest Tools Framework
- Hacking Tools For Windows
- Pentest Tools Bluekeep
- Android Hack Tools Github
- Pentest Tools Nmap
- Hacker Tools Apk Download
- Hack Tools Mac
- Hacking Tools Hardware
- Pentest Tools Alternative
- Pentest Tools Website
- Nsa Hack Tools
- Pentest Tools Github
- Pentest Recon Tools
- Hack Tools Mac
- Pentest Reporting Tools
- Pentest Tools Open Source
- Ethical Hacker Tools
- How To Install Pentest Tools In Ubuntu
- Pentest Automation Tools
- Best Pentesting Tools 2018
- Hack Website Online Tool
- Hacking Tools Name
- Hacker Tools Software
- Pentest Tools Website
- Bluetooth Hacking Tools Kali
- Pentest Tools Android
- Pentest Tools List
- Pentest Tools Bluekeep
- Pentest Tools Framework
- Hacker Techniques Tools And Incident Handling
- Pentest Tools Review
- Hack Tools Download
- Nsa Hack Tools Download
- Best Pentesting Tools 2018
- Hacker Techniques Tools And Incident Handling
- Hack Tools Mac
- Hacking Tools Online
- Pentest Tools Find Subdomains
- How To Make Hacking Tools
- Hack Website Online Tool
- Free Pentest Tools For Windows
No comments:
Post a Comment